Incident Response Engineering
In 1999, Winn Scharwatau released a book entitled "Time-based Security". He argued that time was an essential concept to security, as in 1999, the then zeitgeist was around building impenetrable networks. That was then subsequently penetrated. And he stated, "We should aim to design our networks, with the idea that our defenses will one day fail".
Winn suggested that a simple formula one could use is the time-based security formula.
P>D+R
P – Time taken for an attacker to breach your defenses
D – Time taken for you to detect the attacker
R – Time taken for you to respond to the threat.
While conceptually this formula worked, in 1999, the security community did not have enough information on attackers' behaviors. Furthermore, most networks were flat and unsegregated, which meant that the P time was relatively short, not to mention that detections and responses were in their infancy.
So while it worked in theory, in 1999 it wasn't practical.
However with modern improvements like Cyber Kill Chain, Vulnerability Scanning, MITRE ATT&CK, SOAR and just generally more information, we can have a more meaningful understanding of potential values for P, D & R.
For example, in "Nowhere to Hide, 2021 Threat Hunting Report: Insights from the Falcon OverWatch Team," Crowdstrike analysts looked at the length of time an adversary took in a network before they were able to move laterally. They called this the "breakout time".
They found that the average breakout time was 1 hour 32 minutes in the past year. The report adds that "OverWatch found that in 36% of those intrusions, the adversary was able to move laterally to additional hosts in less than 30 minutes."
Ultimately, we may never know how long an attacker needs to be on our network to achieve their goal; however, we should prioritize improving our incident response to limit their time on our network.
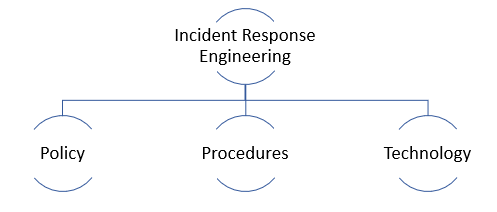
Incident Response Engineering is the discipline of improving your response to a threat.